4,000+ ransomware attacks happen every day. Businesses take about six months to eighteen months to recover from a devastating cyber attack. US businesses suffer losses to the tune of $17 Million per year due to cyber attacks.

With so much of information about cyber security attacks available online, how do these losses keep mounting on a year-on-year basis? Why are businesses and individuals unable to protect themselves from hackers and malicious cyber criminals?
Research has found that 75% of users leave their systems unattended. There is little or no awareness about cyber security attacks and the damage it causes to individual lives and business bottom lines.
All the lack of awareness can also be attributed to the blind belief in myths that have come to be accepted as facts. Here are some such cyber security myths that you need to unlearn and the real facts behind them that you need to learn to become immune to cyber security attacks.
Myth #1: I am a small-scale business, I will not be targeted
When it comes to cyber security, the size of the business makes no difference. Everyone is a potential target. In fact, the real fact behind this myth is that at least 50% of small and medium businesses have experienced a cyber attack of some scale. In fact, a Symantec study also reports that there has been a 43% increase in cyber attacks since 2011.
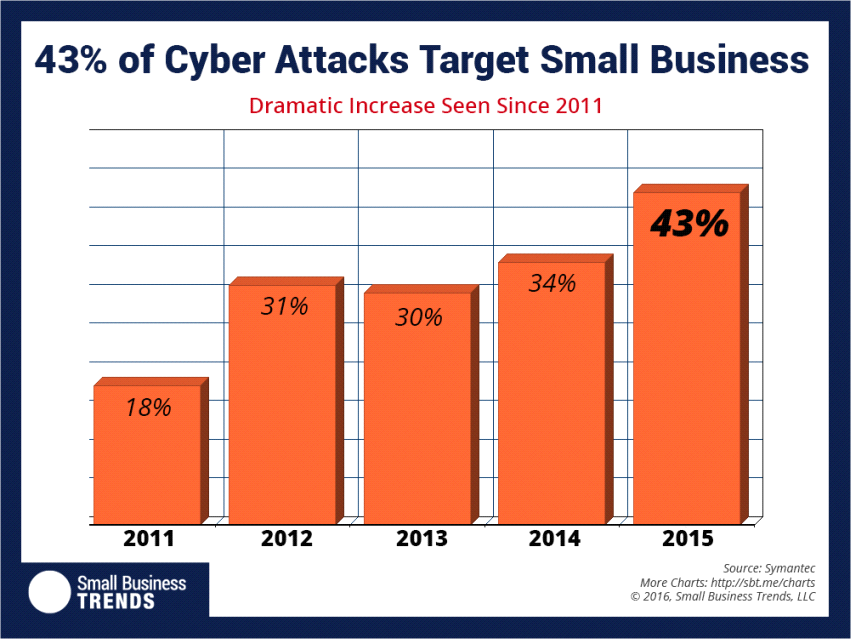
Being small in size and operating with shoestring budgets, they lack the funds to invest in elaborate security measures. So this type of small business should have to look for small budget security measures like Comodo SSL certificates for online information exchange security between server and browser. Even businesses that function as critical data intermediaries for large corporations fail to appreciate the need to invest in serious security measures. This creates a big opportunity for hackers to find their way into the unprotected systems.
Fact:
Small-scale businesses are at a greater risk of being targets for cyber security attacks.
Myth #2: Antivirus takes care of everything
Your antivirus is like the first line of defense. It cannot and does not take care of all your cyber security measures. An antivirus software primarily checks and removes any malicious software or malware from your computer.
It also ensures that any pen drives or external data storage devices that are inserted into the system are also not spreading any virus, bots, worms or Trojan programs that can possibly interrupt your system’s functioning.
An antivirus software does not help to save you from cyber attacks if you fall for any links clicked through social media or email. Also, if you install any pirated software that does not proven publisher details, there is a high chance of having a virus in the disguise of that software. Secondly, if the virus is not yet updated in the antivirus software database, it can penetrate the system and wreak havoc.
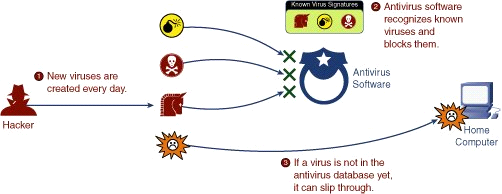
Fact:
Antivirus does not help safeguard yourself from web or external infections.
Myth #3: Desktops are the only devices that get hacked
If it were ten years ago, the fear of virus attacks and data loss were restricted to desktop systems alone. However, in the past ten years so many other devices have also been added to our daily routine.
This includes laptops, tablets, smartphones and so on. Also, there is a new world of Internet connected devices like connected cars, connected manufacturing, connected home appliances, smart home security systems that are also finding their way into our daily lives. The image below shows how much we rely on digital technology:
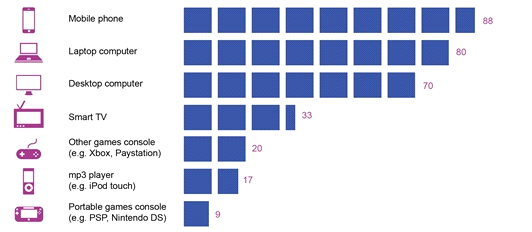
Today, hackers are adept at code injections and hacking procedures that they can infiltrate into any Internet connected device. So, it is not just your desktop systems that are risk prone. If you are connecting to the Internet using any device like tablet, smartphone, IoT Thing, etc. they are also hack-prone.
Fact:
Just like desktop systems, any ordinary device that can connect to the Internet is also hack-prone.
Myth #4: Threat always comes from external sources
According to Ernst & Young, the premier consulting and advisory firm, employees are one of the weakest links in an organization’s cyber security architecture and are often the source of data breaches.”
Lack of awareness leads to bad security practices by employees while dealing with official and practical data. A classic example if public sharing of passwords to critical accounts or software systems.
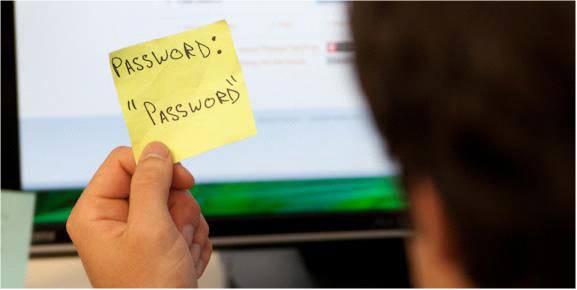
Similarly, exchange of official information through pen drives, external hard drives or insecure cloud servers also lead to security breaches.
Fact:
Employees and insider users can also lead to massive security breaches.
Myth #5: Cyber security criminals target only banks
Cyber security criminals attack every kind of enterprise whose data can help them extort money. Not just banks and financial institutions, but even manufacturing companies (for designs), companies (for undisclosed financial reports), media companies (for unreleased footage), startups (for copyrights, patents, etc.) are also targeted by hackers. Literally, anyone who holds valid data which if made public can cause havoc is a potential target for hackers.
The best way to safeguard such confidential data will be using Comodo Positive SSL which provides 256-bit encryption. Encryption will scramble data exchanged between the user and the server thus preventing the possibility of data loss or security breach.
Fact:
No one is spared by cyber security criminals.
Myth #6: If I don’t click any links, I am safe
It is true that a large proportion of cyber security attacks take place when the user clicks on malicious links that download infected attachments or viruses. However, not clicking on any links does not give the assurance that the user’s system will remain protected from cyber attacks.
Today, hackers hide in plain sight and use simple maneuvers to find their way into the user system. The web browser is often the primary entry point. Outdated browsers are a favorite for hackers since they contain loopholes that can be exploited to gain entry into the system.
Fact:
Clicking or abstaining from clicking links, you are still prone to cyber security attacks.
Winding It Up
Most security breaches are caused not by brilliant hackers by naive myths and those who believe in them. Don’t be one among those naive users. Know the fact from the myth.




