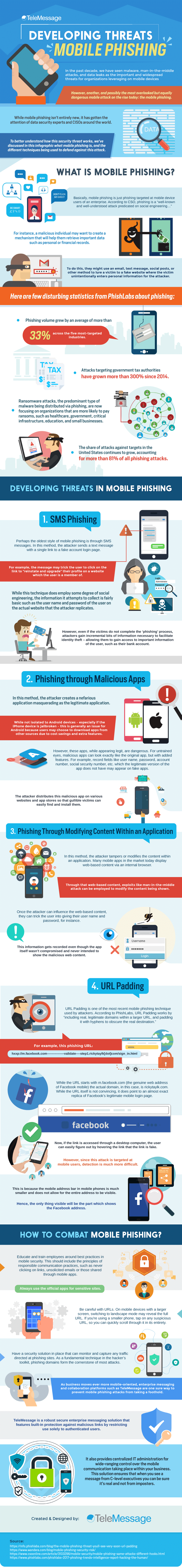
Infographic: Developing Threats in Mobile Phishing
2 minutes | Word Count: 390Different mobile threats are being prominently used to hack personal information and other sensitive content for users today. With the widespread of this profanity, mobile phishing seems to stand out and one of the dangerous mobile attacks today. Mobile phishing is just phishing targeted at mobile device users of an enterprise.
According to CSO, phishing is a “well-known and well-understood attack predicated on social engineering…” For instance, a malicious individual may want to create a mechanism that will help them retrieve essential data such as personal or financial records. To do this, they might use an email, text message, social posts, or another method to lure a victim to a fake website where the victim unintentionally enters personal information for the attacker.
It is best to have a clearer picture of what cases do these things occur, especially when your specific pop-up notifications appear on your mobile. Here are some platforms that are continuously developing mobile phishing:
- SMS Phishing – In this method, the attacker sends a text message with a single link to a fake account login page. For example, the word may trick the user to click on the link to “reinstate and upgrade” their profile on a website by which the user is a member registers their personal information. While this technique does employ some degree of social engineering, the information it attempts to collect is necessary such as the username and password of the user on the actual website that the attacker replicates.
- Phishing through Malicious Apps – In this method, the attacker creates a nefarious application masquerading as the legitimate application. The attacker distributes this malicious app on various websites and app stores so that gullible victims can easily find and install them.
- Phishing through Modifying Content within an Application – In this method, the attacker tampers or modify the content within an application. Many mobile apps in the market today display web-based content via an internal browser. Through that web-based content, exploits like man-in-the-middle attack can be employed to modify the content shown.
Avoiding this mobile phishing threat by having further research about how these programs occur on your devices can give you more maneuver on what to do and report these threats immediately. To learn more about the different mobile phishing threats that could harm your device, check the infographic below created by TeleMessage.